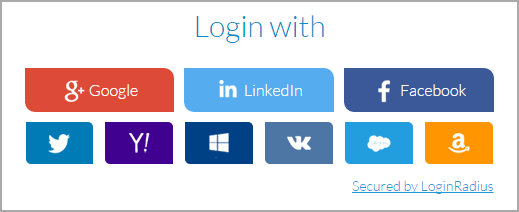
Many websites are offering alternative login methods. This is important since internet security must be our 110% focus these days. Why use them? Google, Facebook, LinkedIn and Microsoft all offer 2-factor authentication meaning that if someone guesses, steals or cracks your password then they still can’t get in to your account without the second piece of authentication (e.g. SMS).
It also helps you from remembering all those individual passwords. I created a document and put all my password and sites on that, and I’m not so trusting of password software to depend on recording those. We have to face the fact that unless we unplug our computers from the internet we’re at one time or another going to be a victim.
Using multi-part authentication is a start and many of the newer programming languages offer the developer to use those technologies right out of the box. On the technical side, authentication tokens are passed back to the asking website from the 3rd party sites (Google, Facebook, LinkedIn, and Microsoft), with a pass or fail, so no important login information is kept and in most cases you define what you want to share with the new site.
Thanks for reading. Remember if you live in the Dallas, Fort Worth area now through the end of 2015 we offer a complete virus removal and system clean up for only $75.00 per computer. Call today 972-571-4808.
-Thanks!!!